The cost amplification problem
Vendor cost rarely grows in a straight line. Each additional tool introduces new integrations, training requirements, administration overhead, and support load. Over time these factors compound.
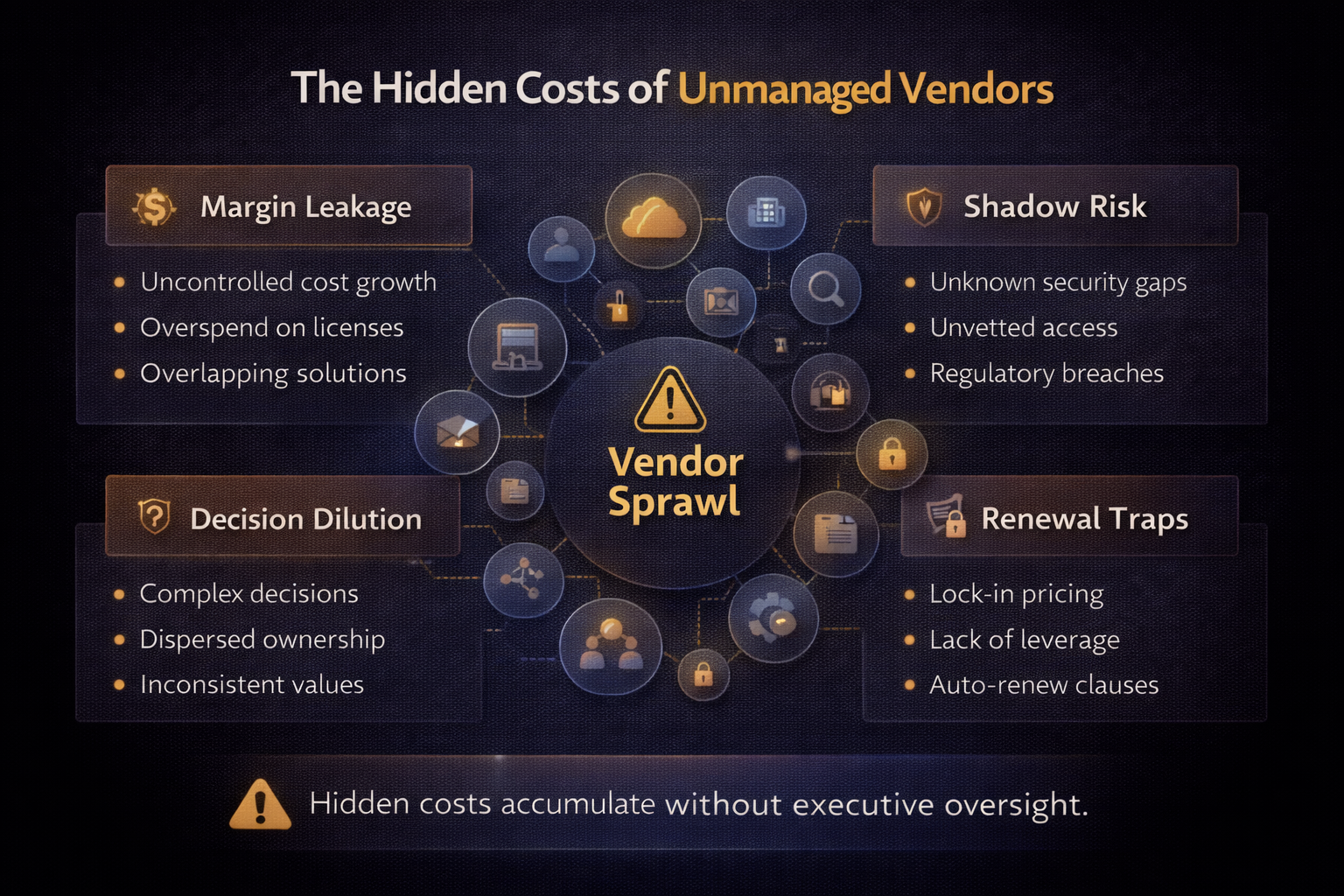
The invoice usually tells only part of the story. The larger cost often shows up in slower decisions, fragmented workflows, more exceptions, and less negotiating leverage. That is why unmanaged vendors quietly affect margin long before leaders see a clear budget alarm.
- Duplicate tools increase fragmentation.
- Integrations multiply across systems.
- Support overhead expands.
- Negotiation leverage declines.
- Risk exposure grows.
Control failure patterns
Vendor sprawl rarely begins as a financial issue. It usually starts as a governance gap. Teams adopt tools to solve immediate problems. The organization accepts the purchase because the local need feels real. A year later the business is funding overlap, complexity, and avoidable dependency.
Diffused ownership
Procurement manages contracts. IT manages integration. Security reviews compliance. Business teams drive adoption. Without a single accountable owner, vendor value becomes difficult to measure and almost impossible to challenge.
Approval gaps
Teams adopt tools independently. Shadow purchasing grows. Security and cost oversight weaken. New tools slip in before leadership understands the long-term support and integration implications.
Renewal drift
Renewals become routine events rather than strategic reviews. Late negotiations reduce leverage. By the time leaders look closely, the vendor is already embedded in workflow and the switching cost feels too high.
Commercial dependency risk
Vendor risk is driven more by dependency than by vendor count. A small number of deeply embedded vendors can create more exposure than a longer list of low-impact providers.
Leaders should evaluate dependency through several lenses and ask where the business would feel the greatest pain if a contract changed, pricing rose, or service quality dropped.
- Data gravity. Critical information sits inside the platform and is hard to extract cleanly.
- Workflow embedment. Teams rely on the platform in daily operational routines.
- Integration footprint. Multiple systems depend on the vendor for process continuity.
- Contract rigidity. Terms make exit, downsizing, or scope changes difficult.
- Replacement market maturity. Alternatives are weak, immature, or expensive to adopt.
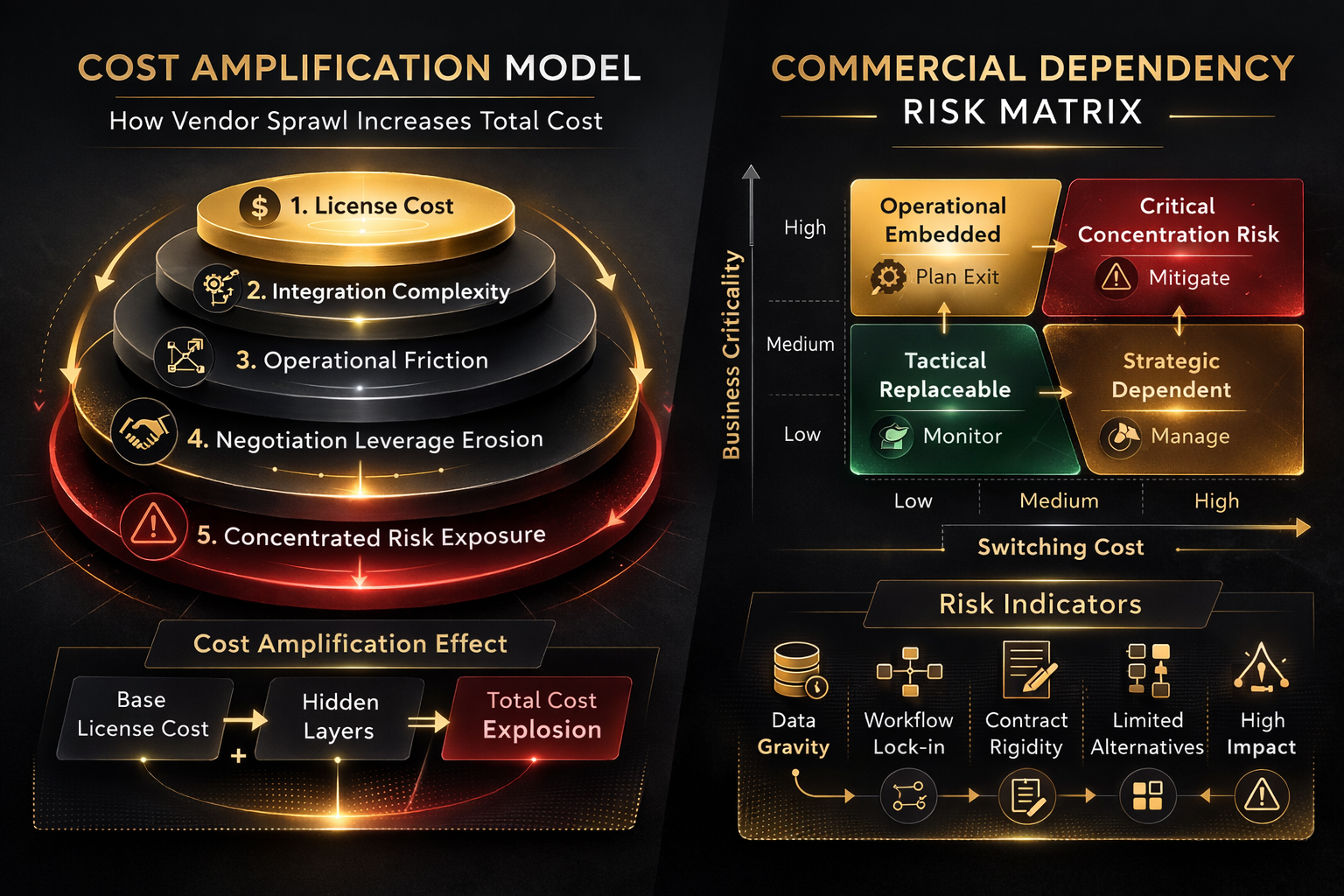
This is where strong vendor oversight connects directly to broader vendor management discipline. The goal is not to eliminate vendors. The goal is to stop uncontrolled dependency from deciding the company’s future choices.
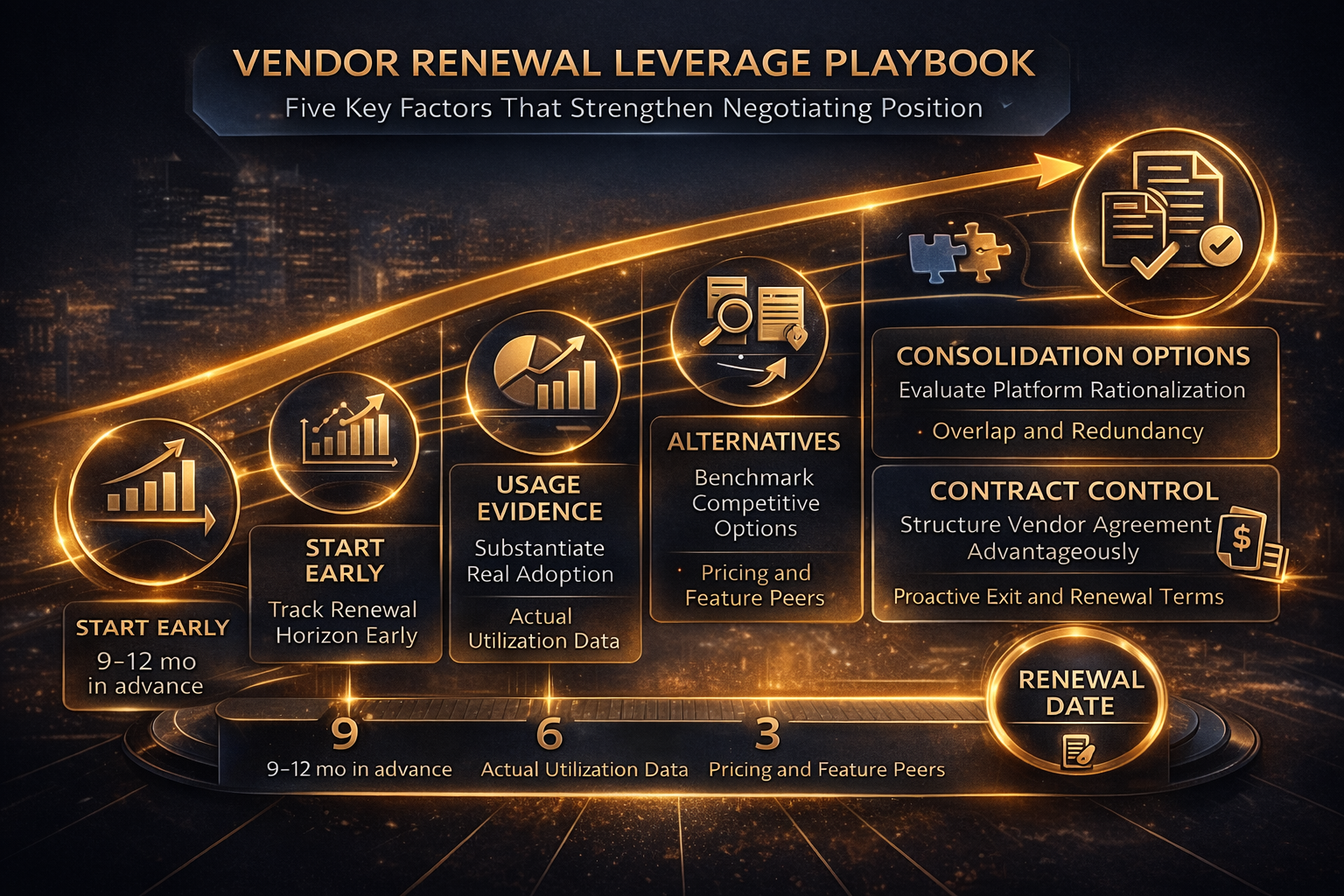
Renewal leverage strategy
Organizations restore leverage when renewals follow a disciplined review process rather than a last-minute scramble. The earlier the review starts, the more options leadership has.
- Maintain a vendor renewal calendar with executive visibility.
- Review usage, adoption, and operational dependence well before the renewal window.
- Benchmark market alternatives and replacement effort.
- Evaluate consolidation opportunities where overlap exists.
- Require a clear owner recommendation before approval.
Strategic vendors should usually be reviewed 120 to 180 days before renewal. That is enough time to challenge pricing, test alternatives, or shape a staged exit if needed.
What executives and boards should see
Boards do not need tool-level detail. They need a clear view of concentration, dependency, renewal timing, and operational impact. Executive reporting should make those patterns visible in one page.
- Vendor spend concentration. How much spend sits with the top providers.
- Dependency exposure. Which vendors hold the most operational leverage.
- Upcoming renewals. Which contracts need decisions in the next 6 months.
- Operational impact. Which vendors create the most support, integration, or continuity risk.
- Mitigation plans. What actions are underway to reduce concentration or improve leverage.
This reporting model works best when it sits alongside a broader execution view such as technology spend aligned to business outcomes. Vendor decisions should support priorities, not operate as a disconnected procurement exercise.
What success looks like in 90 days
Strong vendor governance should produce visible change quickly. If leaders still feel surprised by renewals or cannot explain where dependency sits, the model is too weak.
- Vendor inventory becomes visible and owned.
- Renewal surprises decline.
- Duplicate tools decrease.
- Security and compliance review improves.
- Leadership gains negotiating leverage before major renewals.
Quick answers for executives managing vendors
- Invoice cost is not the full story. Operational drag is often the bigger hidden expense.
- Vendor count matters less than dependency. Deeply embedded vendors create the highest switching risk.
- Renewal timing changes leverage. Review early enough to compare, consolidate, or challenge pricing.
- Governance reduces sprawl. Ownership, thresholds, and cadence keep vendor growth under control.
Frequently Asked Questions
What is the hidden cost of unmanaged vendors?
The hidden cost appears as operational drag. Duplicate tools increase complexity, integrations multiply, and teams spend time managing platforms instead of delivering outcomes.
How early should vendor renewals be reviewed?
Strategic vendors require review at least 120 to 180 days before renewal. Early analysis allows pricing leverage, consolidation opportunities, and alternative evaluation.
What is vendor dependency risk?
Vendor dependency risk occurs when switching costs rise due to integrations, data gravity, workflow embedment, and contract rigidity.
How do organizations stop vendor sprawl?
Assign vendor owners, establish approval thresholds for new tools, maintain a renewal calendar, and review vendor performance quarterly.
What should executives track for vendor governance?
Executives should track spend concentration, dependency risk, renewal timelines, operational impact, and vendor performance metrics.
Need vendor governance without slowing delivery
A focused working session can identify vendor concentration risk, renewal exposure, and governance gaps. Leaders leave with a vendor scorecard, ownership model, and next-step decisions.
Book a consultation