Why risk management breaks down for non-technical leaders
Most leaders do not ignore risk. They lack a simple way to see it and act on it. Teams often bring risk in technical language, then bury it inside project updates, incident notes, and vendor emails. Risk becomes background noise until a disruption forces attention.
Your goal is not to become the engineer. Your goal is to create visibility, ownership, and follow-through. If you do three things well, you will reduce most avoidable risk.
- Make risk visible in plain language.
- Assign one accountable owner per risk.
- Review risk weekly until it closes or is accepted.
This same discipline supports stronger security readiness and better vendor control when technology risk starts to spread across the business.
The six risk categories leaders should watch
Keep the categories small. Leaders lose control when risk is tracked in dozens of buckets.
- Security. Access, vulnerabilities, ransomware, data exposure.
- Reliability. Uptime, incident frequency, recovery capability.
- Compliance. Audit gaps, policy drift, regulatory obligations.
- Delivery. Projects stuck, unclear scope, missed milestones, dependency chaos.
- Vendor. Lock-in, renewals, pricing leverage, support response, exit paths.
- Financial. Spend creep, tool sprawl, hidden run cost, duplicated work.

The one-page risk register leaders should require
A risk register is not a compliance artifact. It is a leadership tool. Keep it short enough that people read it. If it grows, it needs pruning.
Track each risk with five fields.
- Risk statement. One sentence in business language.
- Likelihood. Low, medium, or high.
- Impact. Low, medium, or high. Tie impact to cost, downtime, customer experience, or regulatory exposure.
- Owner. One accountable person, not a team.
- Next action and due date. The next tangible mitigation step and a date.
Add an optional sixth field when needed. Decision required. This forces escalation when the team needs funding, policy changes, vendor support, or a leadership call.
How to prioritize risk without technical detail
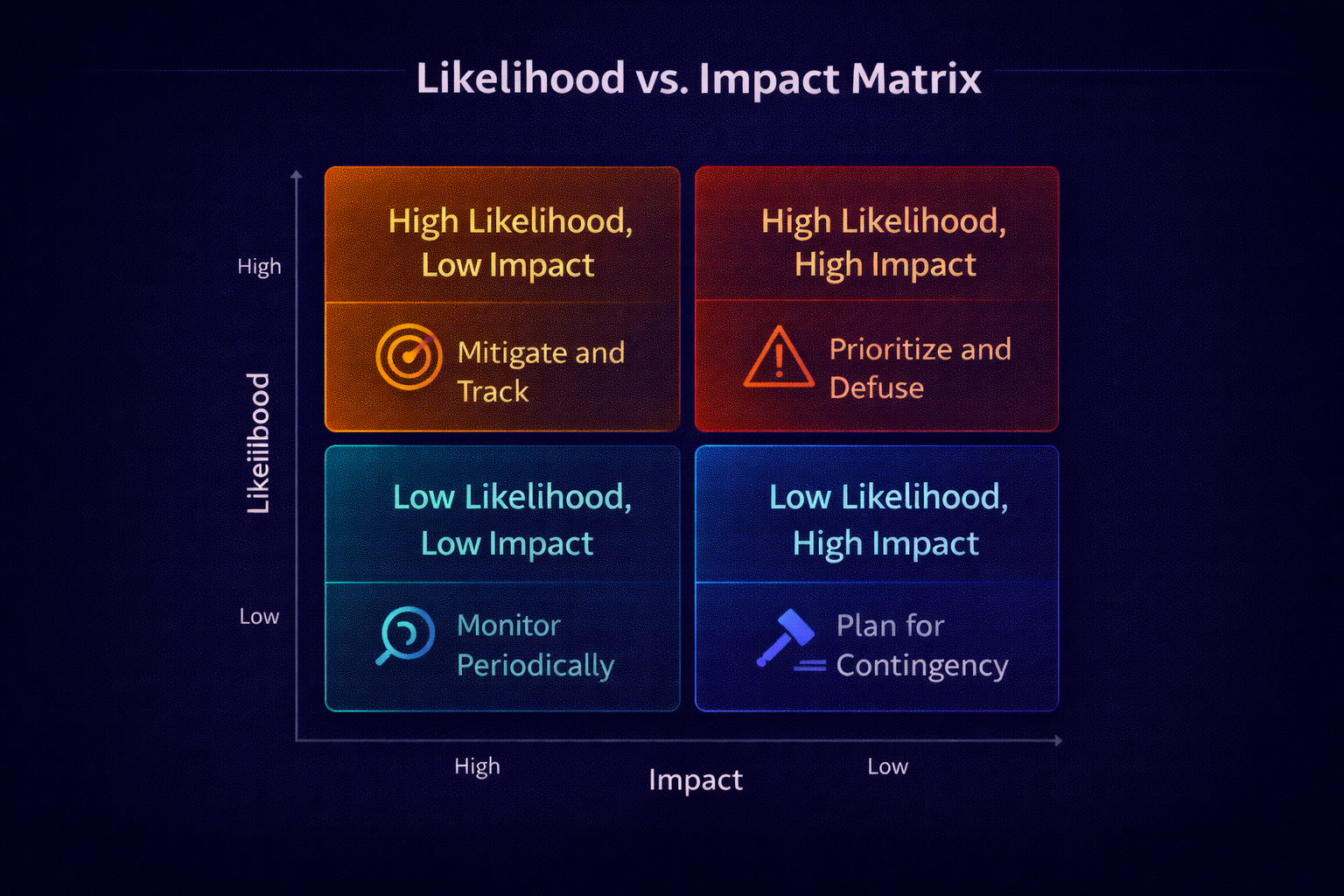
Leaders often ask, “Is this urgent?” Teams respond with technical severity. That misses the business view. Use a simple prioritization method.
- What breaks? Name the business function or customer impact.
- How often? Likelihood based on current trend and controls.
- How bad? Impact in time, money, brand, or compliance.
- Who owns it? If ownership is unclear, risk is automatically higher.
Controls leaders should insist on
You do not need a long list of controls. You need the right few controls executed consistently. These are the controls that reduce the most risk for most organizations.
Security controls
- Multi-factor authentication for all privileged access.
- Quarterly access reviews for critical systems.
- Patching cadence and vulnerability remediation service levels.
- Security awareness and phishing testing.
Reliability controls
- Backups tested with restore drills, not only backup succeeded reports.
- Incident response playbooks with clear escalation.
- Capacity monitoring for systems tied to revenue or operations.
Vendor controls
- Renewal decision matrix. Renew, renegotiate, consolidate, or exit based on outcomes, risk, and adoption.
- Contract terms for support response, data access, and exit rights.
- Quarterly vendor performance review tied to measurable outcomes.
The operating cadence that keeps risk under control
Risk management fails without cadence. Cadence turns intent into behavior. Here is a practical cadence that works for non-technical executives and operational leaders.
- Weekly. 30-minute risk review. Top 10 risks, changes since last week, blockers, and decisions needed.
- Monthly. Executive review. Trend metrics, top vendor risks, top delivery risks, and cost variance drivers.
- Quarterly. Board-ready posture check. Controls health, major incidents, audit posture, and major renewals.

Questions leaders should ask in every risk review
- What changed since last week, and why does it matter?
- Which risks have no owner, and who will own them today?
- Which risks require funding, policy change, or vendor leverage?
- What is the next mitigation step, and when will it complete?
- What is the worst credible scenario, and are we prepared?
90-day risk reset plan
If risk has become reactive, use a short reset plan to rebuild control and confidence.
Days 1 to 30
- Stand up the risk register and assign owners.
- Identify top 10 risks across the six categories.
- Confirm backup restore capability and access controls for critical systems.
Days 31 to 60
- Close the highest-likelihood, highest-impact risks with defined mitigations.
- Implement renewal gates for vendors renewing in the next 120 days.
- Publish a simple metrics view for risk trend and closure rate.
Days 61 to 90
- Institutionalize weekly and monthly cadence.
- Validate incident response and escalation paths with a tabletop exercise.
- Align budgets to risk mitigation priorities and exit plans.
Frequently Asked Questions
Do leaders need technical expertise to manage technology risk?
No. Leaders need clear questions, named owners, simple controls, and a consistent review cadence. The goal is not to become the engineer. The goal is to create visibility, accountability, and follow-through.
What should a simple technology risk register include?
A practical register should include a plain-language risk statement, likelihood, impact, one accountable owner, the next mitigation step, and a due date. Add a decision-required field when leadership action is needed.
Which technology risks should executives watch most closely?
Executives should focus on six categories. Security, reliability, compliance, delivery, vendor, and financial risk. These categories cover most business exposure without creating a complicated tracking model.
How often should leaders review technology risk?
Leaders should review top risks weekly, trend metrics monthly, and overall posture quarterly. Weekly cadence keeps action moving. Monthly review aligns leadership. Quarterly review supports governance and board visibility.
What is the fastest way to improve risk posture in 90 days?
Start a short reset. Stand up a one-page risk register, assign owners for the top 10 risks, verify core controls like access reviews and backup restore capability, and run a weekly review until risk closure becomes routine.
Want a risk posture leaders can run
If your risk conversations feel technical, stalled, or reactive, a short working session can translate risk into plain language, assign ownership, and set a cadence your leadership team will keep.
Book a consultation